Palo Alto Traffic log - Incomplete or Insufficient data
The Application Field can show you one of the following entries: Not-Applicable, Incomplete, Insufficient Data.
Ever wondered what the different entries in the traffic log - “Application Field” mean? The following can show up inside of the Application field:
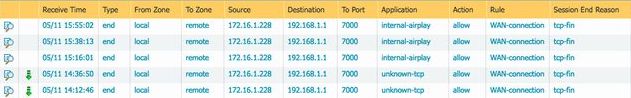
These are the most occurring entries:
- Incomplete
- Insufficient data
- Not-applicable
- unknown-tcp
Application Field: Incomplete
"Incomplete" means that "either the three-way TCP handshake did not complete" or "the three-way TCP handshake **did** complete
but there was no data after the handshake to identify the application."
It means: that the traffic being seen is not really an application.
Example:
A client sends a server a SYN and the Palo Alto Networks device creates a session for that SYN,
but the server never sends a SYN ACK back to the client, then that session is incomplete.
Application Field: Insufficient data
"Insufficient data" means that there is not enough data to identify the application.
Example:
If the three-way TCP handshake completed and there was one data packet after the handshake, but that one data packet was not enough
to match any of the Palo Alto signatures, then the user will see “insufficient data” in the application field of the traffic log.
Application Field: Not-applicable
"Not-applicable" means that the Palo Alto Firewall has received data that will be discarded because the port or service that the traffic is coming in on was not allowed.
Or there is no policy allowing that port or service.
Example:
If there is only one rule on the Palo Alto Firewall and that rule allow’s the application: web-browsing but only on port 80, and traffic (web-browsing or any other application) is sent to the Palo Alto Firewall on any other port besides port 80, then the traffic is discarded or dropped.
Therefor you will see “not-applicable” in the application field.
Application Field: unknown-tcp
"Unknown-tcp" means that the firewall has captured the three-way TCP handshake, but no application could be identified.
This may be due to the use of a custom application for which the firewall does not have any signatures.
← →